Battles are being fought in the field, and you are looking for the tool for winning it- Field Intelligence!
Modern Management sciences have established that Organization needs to view itself as the support for the field warriors, facing customers and fighting battles.
In this light, it is crucial that Organization’s practices, decisions and actions are oriented to support what is happening on the field. And therein lies the question- What is happening in the field?
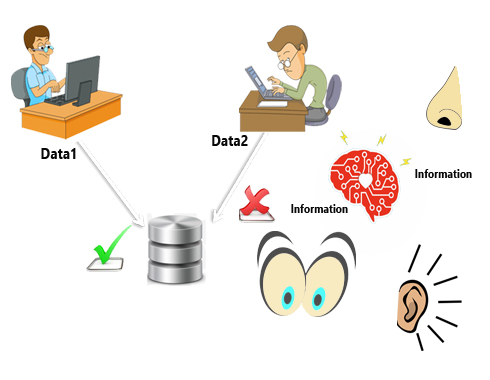
Without accurate, authorized, reliable, timely and relevant information flowing into decision making arms of the Organization, the battle is already lost, as most managers will vouch for this fact.
But how to provide a mechanism to gather structured and unstructured actionable intelligence from the field? Well, just to add to it, in a cost
effective and timely manner too.
If this has your attention, you already recognize why this is crucial and may be you’d like to read a bit further below.
Field Events are the buzz word today, but an effective strategy to deliver intelligence must address several issues including the following:
- Authorization: The events reported are often mission critical and authorization is often a requirement to be applied not only based on event type, but who can report what type of data.
- Multi Protocol Support: In quest for gathering as much data as possible, a key issue is to provide multiple, easy to use channels to report data. Hence any strategy for event data collection must support multiple protocols and provide easy options for reporting events from field.
- Chaffing out erroneous events: Field data, when used for decision making can actually make decisions suboptimal if quality of data is poor. Hence it is crucial to incorporate functions that can automatically recognize erroneous data and chaff out for either rejection or correction as the case may be (depending on data type).
- Workflow before accepting events: When field events are not just used for statistical support purposes, but are mission critical information, such as demand forecast, then often system must provide ability to manually calibrate before data is accepted for processing.
- Customization of channels: Different channels for reporting have different costs, accessibility and criticality. Hence often system must provide ability to customize channel allocation to different field users.
- Data Level Security: Sometime authorization at type of information is not enough, but additional data level security for access and reporting must additionally be provided. For example, a field executive can only place orders in a certain sales territory or for a certain product, but not for others. Ability of a system to provide such data level security controls is thus a key issue for many applications.
- Low Cost Framework: Given the vast number of applications and kinds of field data available, it is a key issue to have a low cost system that enables different kind of events to be quickly added for various kinds of analysis, processing in business applications.
- Audit Record: While a large number of event accumulator applications exist, often an audit trail is a key issue when event is not simply a volatile statistical data. Thus any strategy must address this as a key issue.
- High volume handling: As per principles of statistics, higher the volume, more accurate the results in statistical applications. Thus strategy must employ an approach to use NoSQL databases with horizontal scaling in a distributed environment for addressing such issues.
- Patterns and alerting: The data is only as good as what application can make of it! Hence systems must incorporate functions that allow for quick pattern recognitions and action functions to be define on it.
Our platform Event Management Framework is geared to address all of these issues highlighted effectively, as following notes describe.
Authorization:- EMF uses a concept of meta fields in events being reported and provides framework for filtering out undesired events both at enterprise level as well as at user level. Thus delivering total control of processing behavior authorization without coding.
- EMF provides a built in Authorization framework that enables data level authorizations to be defined for various users, thus providing a strong, pre-built authorization framework that can be readily used for solutions without coding. The features enable authorizations that restrict at data level what kind of data is accepted by the solution, who gets to send what data and via what protocol, thus providing a feature rich pre-built platform to implement any level of authorizations.
- With workflow, custom orchestration, business rule engine, EMF allows for Enterprise class processes to be defined quickly and made available for use. With strong customization framework a developed application process can be customized for your use with least effort.
- EMF comes bundled with various technologies that enable solutions to cover various features including alerting, workflows, drill down reports and mashups, mobile apps etc thus enabling to introduce a feature rich solution from the word go.
- EMF provides pluggability of validation and enrichment rules in the system before the data is processed as validated data thus enabling a strong pre-built layer to control quality of data at source before it can be used as basis of decision making.
- EMF uses a unique approach where bulk of the UI is pre-built in a UI framework and functions regardless of the solution, the framework provides sockets for solution specific screens to be plugged in. Thus UI development time is significantly reduced and limited to writing solution specific individual pages rather than having to design a detailed UI framework.
- EMF has a strong focus to support multiple protocols for inbound data collection including mobile channels. Thus supporting your enterprise mobility objectives from the word go. These channels support is pre-built thus enabling Enterprise Mobility at low cost and low time to market.
- EMF uses NoSQL database and closely integrated BAM engine to allow for volume handling as well as pattern analysis, proactive alerting on trends, rule based threshold breaches. Thus EMF enables BIG data applications to be defined quickly and delivered leveraging existing functions and components.
